Development
Why Choose a Bespoke WordPress Theme Over a Template?
Discover why choosing a bespoke WordPress theme over a template can boost performance, SEO, and flexibility for your growing business.
20th April, 2025
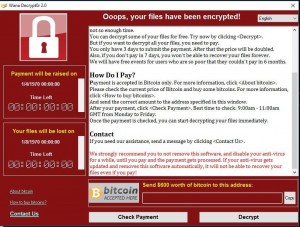
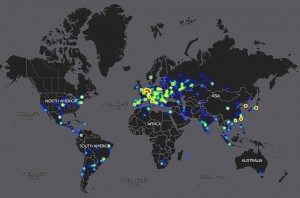
On the 12/05/2017 one of the biggest cyber-attacks quickly spread over the world, causing a crisis in National Health Service hospitals and some of Europe’s biggest businesses. The new strain of ransomware WannaCry (also known as WanaCrypt0r and Wcry) is a malware that usually locks users out of their own system (usually by encrypting the data on the hard drive) and then holding the decryption, or another release key, ransom until the victim pays the fee. The fee is usually in bitcoin, due to it being hard to track.
In this case, the NHS experienced massive failure of their computer and phone systems, this caused widespread confusion as the computers started to show a ransom message demanding $300 bitcoin. As a result of Friday’s cyber-attack, hospitals, doctors’ offices, and other healthcare institutions, all over the UK had to cancel non-urgent services and start the backup procedures. Multiple emergency rooms spread the word that patients should avoid coming in, if possible. It was all a bit of a mess. Although, no unauthorised access to patient data has been affected so far.
Cybersecurity experts said the ransomware works as a malware which could spread through computers with unpatched Microsoft Windows. The vulnerability (MS17-010) affects Microsoft Windows Vista, 7, 8, 10, XP and versions of the Windows Server software. They urged that all computers still running this software should run their computers in ‘safe mode’ until they have checked the update blocking the ransomware is installed.
The exploit was released a month ago by a hacking group, Shadow Brokers, in a trove of alleged NSA tools. However, Microsoft released a patch for the exploit, known as MS17-010, in March, but clearly many organisations haven’t caught up, despite the warning. So, should this have been avoided?
Marcus Hutchins was to thank for slowing down the infamous WannaCry malware, as he discovered the so-called “kill switch”, but said, “I’m definitely not a hero”. The 22-year-old works for Los Angeles-based Kryptos Logic security company, who took over the kill switch Friday afternoon, before the virus could fully affect the USA. But added the malware was “poorly designed” – patched together and a “sum of different parts” with an unsophisticated payment system.
If a patched together malware can do this much damage, is this just the first of many major cyber-attacks that we will see happen this year? I believe so, as Bitdefender has already reported having seen a new version of the WannaCry ransomware with the kill switch removed. Let’s hope businesses take this as a warning to take security seriously.
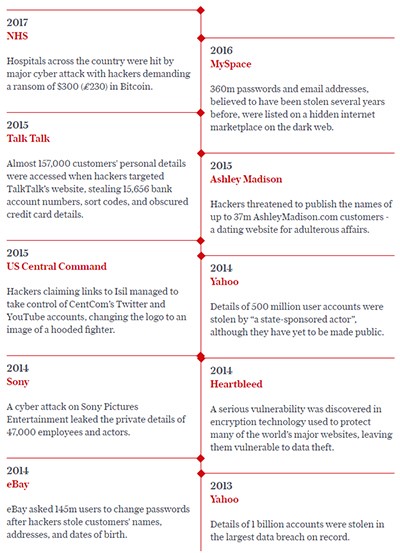
Here’s a timeline of the major hacks over the last few years, some for which you may not have heard about:
Development, Our News
17th May, 2017
Call us on: +44 (0) 161 941 5330 or email us: info@firstinternet.co.uk
Get in touch today!